hello India,
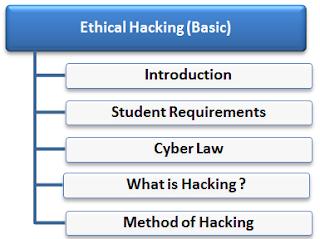
so guys today i'm going to share some info about cyber laws in India.
In Simple way we can say that cyber crime is unlawful acts wherein the computer is either a tool or a target or both
Cyber crimes can involve criminal activities that are traditional in
nature, such as theft, fraud, forgery, defamation and mischief, all of
which are subject to the Indian Penal Code. The abuse of computers has
also given birth to a gamut of new age crimes that are addressed by the
Information Technology Act, 2000.
We can categorize Cyber crimes in two ways
The Computer as a Target :-using a computer to attack other computers.
e.g. Hacking, Virus/Worm attacks, DOS attack etc.
The computer as a weapon :-using a computer to commit real world crimes.
e.g. Cyber Terrorism, IPR violations, Credit card frauds, EFT frauds, Pornography etc.
Cyber Crime regulated by Cyber Laws or Internet Laws.
Technical Aspects
Technological advancements have created new possibilities for criminal
activity, in particular the criminal misuse of information technologies
such as
a. Unauthorized access & Hacking:-
Access means gaining entry into, instructing or communicating with the
logical, arithmetical, or memory function resources of a computer,
computer system or computer network.
Unauthorized access would therefore mean any kind of access without the
permission of either the rightful owner or the person in charge of a
computer, computer system or computer network.
Every act committed towards breaking into a computer and/or network is
hacking. Hackers write or use ready-made computer programs to attack the
target computer. They possess the desire to destruct and they get the
kick out of such destruction. Some hackers hack for personal monetary
gains, such as to stealing the credit card information, transferring
money from various bank accounts to their own account followed by
withdrawal of money.
By hacking web server taking control on another persons website called as web hijacking
b. Trojan Attacks:-
The program that act like something useful but do the things that are
quiet damping. The programs of this kind are called as Trojans.
The name Trojan Horse is popular.
Trojans come in two parts, a Client part and a Server part. When the
victim (unknowingly) runs the server on its machine, the attacker will
then use the Client to connect to the Server and start using the trojan.
TCP/IP protocol is the usual protocol type used for communications, but
some functions of the trojans use the UDP protocol as well.
c. Virus and Worm attack:-
A program that has capability to infect other programs and make copies of itself and spread into other programs is called virus.
Programs that multiply like viruses but spread from computer to computer are called as worms.
d. E-mail & IRC related crimes:-
1. Email spoofing
Email spoofing refers to email that appears to have been originated from
one source when it was actually sent from another source. Please Read
2. Email Spamming
Email "spamming" refers to sending email to thousands and thousands of users - similar to a chain letter.
3 Sending malicious codes through email
E-mails are used to send viruses, Trojans etc through emails as an
attachment or by sending a link of website which on visiting downloads
malicious code.
4. Email bombing
E-mail "bombing" is characterized by abusers repeatedly sending an identical email message to a particular address.
5. Sending threatening emails
6. Defamatory emails
7. Email frauds
8. IRC related
Three main ways to attack IRC are: attacks, clone attacks, and flood attacks.
e. Denial of Service attacks:-
Flooding a computer resource with more requests than it can handle. This
causes the resource to crash thereby denying access of service to
authorized users.
Our support will keep you aware of types of Cyber crimes while companies
such as www.Lifelock.com can give you the right protection against
them.
Examples include
attempts to "flood" a network, thereby preventing legitimate network traffic
attempts to disrupt connections between two machines, thereby preventing access to a service
attempts to prevent a particular individual from accessing a service
attempts to disrupt service to a specific system or person.
read more
 and click on button Online on the right side of the page. We will do best to help you as soon as possible.
and click on button Online on the right side of the page. We will do best to help you as soon as possible. and click on button Online on the right side of the page. We will do best to help you as soon as possible.
and click on button Online on the right side of the page. We will do best to help you as soon as possible.